Table of Contents
Introduction
DMARC requirements now decide whether your emails reach the inbox or get silently rejected, even when SPF and DKIM are already set up.
Most teams assume they’re compliant because their DNS records look correct. But DMARC doesn’t evaluate configuration. It evaluates how each email is actually sent. That’s why the same campaign can pass in one system and fail in another without any visible warning.
In real environments, especially with Salesforce, email execution is rarely centralized. Data lives inside the CRM, but emails are sent through multiple tools, marketing platforms, automation systems, and relays. Each path can change the sending domain, authentication method, or alignment behavior. Even small inconsistencies at send time are enough to fail DMARC.
This guide breaks down what actually drives DMARC outcomes: sending behavior, not setup. You’ll learn what Google and Yahoo expect, where real-world implementations fail, how to validate compliance across systems, and how to fix alignment issues without breaking legitimate email flow.
What Are DMARC Requirements for Google and Yahoo Bulk Senders?
DMARC requirements from Google and Yahoo mean your emails must pass authentication and domain alignment checks at send time, based on how each message is actually sent, not just whether your DNS records exist.
1. DMARC requirements for Google bulk senders
Google requires bulk senders to prove identity and maintain consistent sending behavior across every email path. In practice, you must authenticate emails using SPF or DKIM, publish a DMARC record, and ensure the visible “From” domain aligns with the authenticated domain at send time.
Sending patterns also influence evaluation. Sudden changes in domains, tools, or volume introduce risk signals, while user actions like spam complaints directly affect how providers treat your emails.
“Bulk sender” extends beyond large campaigns. If Salesforce data triggers emails across marketing tools, automation systems, or notifications, you operate at a bulk scale. Because of this, the same campaign can pass DMARC in one system and fail in another, since each path handles domains and authentication differently.
2. DMARC requirements for Yahoo bulk senders
Yahoo follows a similar baseline but places stronger emphasis on consistent sender accountability across all email sources. Emails must be authenticated and clearly tied to a verifiable domain, while DMARC must be published for domains used in ongoing email programs. In addition, sender identity must remain stable across campaigns, tools, and message types, since inconsistency across systems is treated as a trust issue.
Even if your audience is Gmail-heavy, Yahoo still matters. Business recipients use multiple mailbox providers, so compliance designed only for Google often breaks when the same emails are evaluated by Yahoo’s systems.
3. What “DMARC required” actually means in practice
In reality, “required” does not apply equally to every sender, but enforcement risk increases with visibility and scale. High-volume senders are directly evaluated against provider expectations, while moderate-volume senders still face alignment and trust checks across campaigns and automations. Even lower-volume senders using branded domains are not exempt, because misalignment still affects inbox placement and future scalability.
More importantly, early infrastructure decisions create long-term impact. When emails are sent through multiple tools with different domain setups, inconsistencies may go unnoticed at low volume but become difficult to fix as sending grows.
4. Minimum DMARC policy required to stay compliant
Publishing a DMARC record is only the starting point. A policy such as p=none enables visibility into authentication results without enforcing rejection. While this may satisfy record-level expectations, it does not prevent misaligned emails from being treated as untrusted.
As a result, if different systems send emails with inconsistent domain alignment, p=none only exposes the issue rather than resolving it. This is why many teams believe they are compliant while still experiencing inconsistent inbox placement. Ultimately, DMARC requirements are enforced on sending behavior, not just configuration.
How DMARC Requirements Work Without the Technical Overload
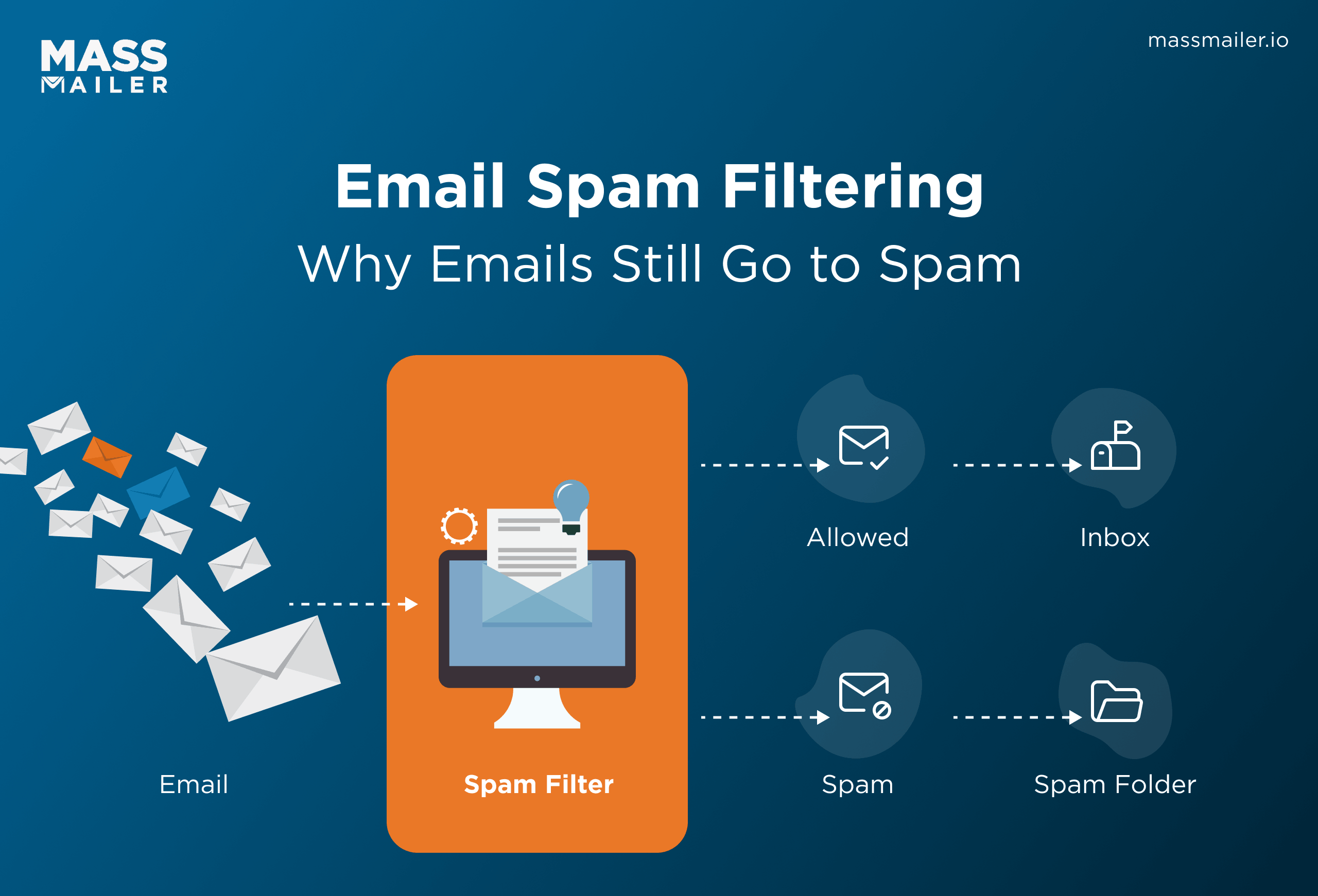
DMARC works by checking whether an email passed authentication in a way that matches the visible sender domain, and then telling mailbox providers how to handle failures.
1. How SPF, DKIM, and DMARC connect during email authentication
Every email goes through a simple but strict check. The receiving server evaluates who sent the email, whether the message is trustworthy, and whether that identity matches what the recipient sees. DMARC sits on top of this process and decides whether the authentication results actually count for the sender being presented.
- SPF verifies whether the sending server is authorized for a domain
- DKIM verifies whether the message is signed by a domain and has not been altered
- DMARC checks whether SPF or DKIM passed in alignment with the visible “From” domain
- A message can pass SPF or DKIM and still fail DMARC if alignment breaks
- DMARC turns authentication signals into a pass/fail decision tied to sender identity
2. What alignment means and why most DMARC failures happen
Alignment means the domain in the visible “From” address matches, or properly aligns with, the domain validated by SPF or DKIM. This is where most DMARC failures occur. Many teams configure all required records, but still fail because the tool that sends the email uses a different domain than the one the recipient sees.
- The “From” domain must align with the SPF-validated or DKIM-signed domain
- Many failures happen even when SPF, DKIM, and DMARC records exist
- A common failure pattern is authenticating one domain while displaying another
- This often happens across Salesforce, marketing platforms, notification tools, or mixed subdomain setups
- DMARC usually breaks at send time, not at setup time
3. How DMARC policy controls what happens after authentication
After DMARC evaluates authentication and alignment, it instructs the mailbox provider how to act on failures. This decision directly affects whether emails are delivered, filtered, or blocked, which means policy strength must match how well your sending environment is understood.
- p=none allows emails to pass while exposing authentication and alignment gaps
- p=quarantine pushes failing emails toward spam or restricted placement
- p=reject blocks failing emails from being accepted
- Stricter policies increase the risk of affecting legitimate emails if alignment is inconsistent
- DMARC policy decisions influence both spoof protection and valid email delivery outcomes
Why DMARC Requirements Fail in Real Sending Environments
DMARC requirements fail when different systems send the same domain in different ways. Records may exist, but each email is evaluated at send time, and inconsistent execution breaks alignment.
This is a common scenario shared on Reddit:
“Salesforce emails get sent through our MS Exchange server; however, if we set out a DMARC policy to reject, they get rejected by the recipient. Does anyone have a solution ?”
This pattern appears often. Emails seem to work until stricter DMARC enforcement is applied. Once the policy moves to reject, hidden alignment issues surface. In setups where Salesforce sends through Exchange, the visible sender domain and authentication domains often differ. As a result, DMARC fails at send time, and the receiving server rejects the email.
1. Multiple email tools use different sending domains
Most teams send emails through multiple systems. Salesforce, marketing platforms, support tools, and billing systems all handle sending differently. Each tool uses its own DKIM domain, return-path domain, or subdomain.
The visible “From” domain may stay consistent, but backend authentication varies. As a result, one system can pass authentication while another fails for the same brand. This creates coordination overhead and makes alignment unpredictable. When systems operate independently, the issue becomes structural rather than a simple configuration gap.
2. SPF fails when too many services are added
Teams add sending services over time, and each one expands the SPF record. As the record grows, it eventually exceeds lookup limits. When that happens, SPF fails even though all services were added correctly.
These failures often go unnoticed because sending appears normal from the outside. Old or unused services also remain in the record, increasing complexity. As SPF becomes harder to maintain, the system relies entirely on DKIM.
This creates risk because every sending path must now sign correctly without exception.
3. DKIM is configured for some flows, but is missing in others
Teams usually configure DKIM for primary campaigns but overlook other flows. Automated emails, alerts, and legacy systems often remain unsigned or use vendor domains. This creates inconsistent authentication results across email types.
High-volume campaigns may pass, while lower-volume operational emails fail. These gaps are easy to miss because teams validate only the most visible flows. However, DMARC evaluates every email independently.
A single unsigned or differently signed flow is enough to create inconsistent outcomes.
4. Domains do not align between “From”, SPF, and DKIM
DMARC requires the visible sender domain to align with authentication domains. Many setups break this requirement because different layers use different domains. The “From” address may show one domain, while DKIM signs with another.
The return-path domain may also differ. Subdomains often vary across tools without coordination. Branding decisions focus on the visible sender but ignore backend authentication domains. Delegated or outsourced sending adds further variation.
When these domains do not align, authentication results no longer support the sender identity.
5. DMARC records exist, but teams do not monitor them
Many teams publish a DMARC record and assume the work is complete. Without monitoring, the record becomes passive rather than protective. Teams do not review authentication outcomes, so unauthorized senders remain undetected.
Legitimate emails may fail without visibility, and stricter policies become risky without data. Issues persist because no feedback loop exists to identify failures. Without monitoring, teams cannot see which systems break alignment or how problems evolve.
How to Validate DMARC Compliance Before Enforcement
You validate DMARC compliance by confirming that real emails pass authentication and alignment across every sending path, not by relying on DNS records alone.
1. How to locate and verify your DMARC DNS record
A DMARC record is valid only if it is publicly queryable, correctly placed, and syntactically accurate.
Check that the record exists at _ dmarc.yourdomain.com, resolves without errors, and includes a clear policy value. Confirm that reporting tags are present if you expect visibility into failures. Many records fail because they are added to the wrong host, contain formatting issues, or never propagate externally.
A valid record only tells mailbox providers what to do. It does not confirm that your emails follow that policy when sending.
2. How to read DMARC reports to detect alignment failures
DMARC reports are useful only when you extract patterns, not when you read them line by line.
Identify which systems send on your behalf, which sources consistently fail, and where alignment breaks. Focus on repeated failures from legitimate systems. These indicate structural gaps in how emails are sent, not isolated issues.
Reports often surface systems you did not account for. They expose operational reality, including tools, integrations, and services that are sent under your domain without clear ownership.
3. How to identify unknown or unauthorized sending sources
Unknown senders appear because email ecosystems grow faster than governance.
Look for sources tied to old tools, third-party integrations, regional systems, or temporary automations. For each sender, determine whether it is expected, unnecessary, or suspicious. This classification matters because DMARC enforcement acts on all traffic, not just your primary campaigns.
Most teams validate their main sending system and miss secondary flows. Those gaps become the first point of failure when enforcement increases.
4. Tools and methods to validate SPF, DKIM, and DMARC together
DMARC validation is reliable only when it reflects real message behavior across systems.
Use DNS lookups to confirm records exist. Inspect headers from actual emails to verify SPF, DKIM, and alignment results. Review DMARC reports to understand behavior across all sources. Test emails from each system to confirm consistent outcomes.
Each method answers a different question. DNS shows configuration. Headers show per-message results. Reports show ecosystem-wide behavior over time.
Most teams validate one tool and assume global compliance. DMARC does not work that way. It evaluates each message independently, so validation must cover every sending path.
Step-by-Step Approach to Meeting DMARC Requirements Without Breaking Email Flow
You meet DMARC requirements by fixing authentication across all senders, validating real traffic, aligning domains, and enforcing policy in controlled stages.
DMARC failures rarely come from missing records. They come from inconsistent execution across systems.
1. Setting up SPF and DKIM correctly across all sending sources
Start by mapping every system that sends email using your domain. Most teams configure authentication for their main campaign tool but miss secondary flows such as CRM alerts, support systems, or billing notifications.
Assign each sender a clear authentication method and domain strategy. Keep SPF entries controlled and within lookup limits to avoid silent failures as more services are added. Enable DKIM for every sending platform using domains that match your visible sender identity.
DMARC stability depends on consistency across all flows. One correctly configured system does not compensate for another that sends unsigned or misaligned email.
2. Starting with monitoring mode (p=none) and analyzing reports
Use monitoring mode to observe how your email behaves across all systems before enforcing restrictions. This stage reveals real sending patterns without affecting delivery.
Identify all legitimate sources, measure pass rates, and detect alignment gaps. Monitoring is not a waiting period. It is how you uncover hidden dependencies and unexpected sending paths.
Teams often publish DMARC and assume they are compliant. That assumption fails because enforcement decisions require evidence from real traffic, not configuration alone.
3. Fixing alignment issues before enforcing stricter policies
Alignment must hold between the visible “From” domain, the DKIM signing domain, and the SPF-authenticated return-path domain. Most failures occur when these domains differ across systems, even when authentication exists.
Standardize domain usage across all platforms. Replace default vendor domains, align subdomain strategies, and remove systems that cannot meet alignment requirements.
Alignment failures often reflect ownership gaps across teams and vendors. When each system follows a different domain model, DMARC breaks at execution time.
In Salesforce-driven environments, this problem becomes more visible because data and triggers live inside the CRM, while email execution happens across external tools.
Salesforce-native tools like MassMailer help reduce this gap by keeping sending behavior closer to the source system, which improves alignment consistency without introducing additional execution layers.
4. Gradually moving to quarantine and reject without blocking valid emails
Increase policy strength only after legitimate traffic consistently passes DMARC. Move to quarantine once failure patterns are understood and alignment is stable. Move to reject only when you are confident that valid emails will not fail.
Each step must be evidence-driven. Legitimate sources should be fully identified, authentication should be consistent, and unexpected failures should be resolved before escalation.
A common mistake is moving to reject because DNS appears complete. DMARC enforcement evaluates live message behavior, not how records look in configuration.
5. Standardizing email sending across tools, CRMs, and platforms
Long-term DMARC stability depends on how email is executed, not just how it is configured. Organizations that send from multiple tools without coordination reintroduce alignment issues with every new system.
Reduce independent sending paths and define clear rules for domain usage and authentication. Ensure new tools follow the same standards before they send an email.
In Salesforce-heavy environments, this is where execution often breaks. Data lives inside Salesforce, but emails are sent through multiple external tools, each using different domains, authentication setups, and sending logic. This creates alignment drift even when records are correctly configured.
MassMailer addresses this by executing email directly inside Salesforce using a single, controlled sending path. Instead of splitting execution across systems, emails follow one consistent authentication and domain model at send time. That consistency removes the variability that causes DMARC failures across tools.
DMARC is not a one-time setup. It is a governance model for how your organization sends email. Without standardization, every new tool reintroduces risk. With it, compliance becomes repeatable instead of reactive.
Conclusion
DMARC requirements are simple on paper, but fail in practice because email is sent through multiple, inconsistent systems.
You now know the path: understand provider expectations, ensure alignment, identify failure patterns, validate real traffic, and enforce policy in stages. Publishing a DMARC record is not compliance. Consistent execution across every sending path is.
Start by reviewing all sending sources, confirming alignment in real emails, and removing fragmented execution before tightening policy. DMARC is an ongoing operational discipline, not a one-time setup.
If your Salesforce environment drives most communication, consider exploring a MassMailer demo to see how a single, aligned sending path can simplify compliance and reduce execution risk.
Frequently Asked Questions
1. Do DMARC requirements differ between Google and Yahoo?
2. Can emails pass DMARC if SPF fails?
3. Does DMARC affect email deliverability directly?
4. Is a DMARC record required for all domains?
5. What happens if DMARC fails?
6. How long does it take to become DMARC compliant?
Start Your Free Trial Today
Experience MassMailer the easiest way to send personalized emails from Salesforce.
Related Blogs
MassMailer Resources